Quantum VPN
Post-Quantum Security
Hybrid cryptography combines post-quantum algorithms with RSA and ECC, ensuring compatibility with existing systems while delivering quantum-resistant protection.
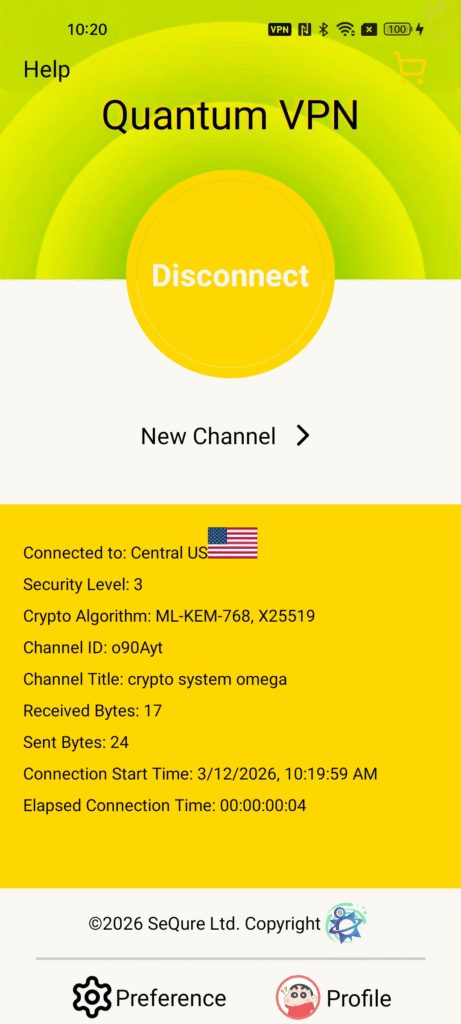
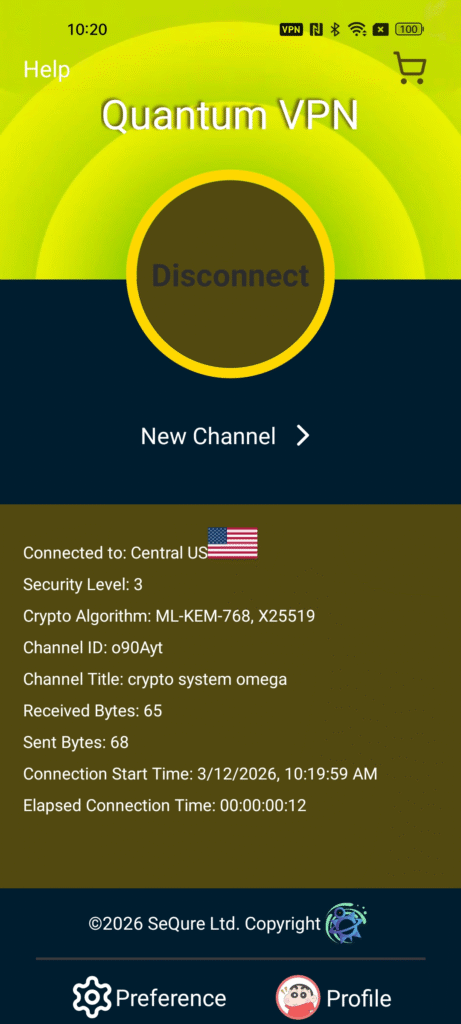
Intelligent Cryptographic Optimization
An adaptive optimization engine dynamically balances security strength and computational efficiency across different deployment scenarios.
Global Low-Latency Network
A distributed cloud service mesh connects users through the nearest available nodes, reducing latency and improving cross-border communication performance.
High-Performance Encryption Engine
GPU acceleration and high-performance infrastructure significantly improve the efficiency of key generation, encryption, and digital signature verification.
Use Cases

Organizations
Secure communication infrastructure for institutions and government agencies, enabling remote users to access self-hosted services and conduct confidential meetings through encrypted VPN tunnels.

Individual Users
Private peer-to-peer communication for individuals across different locations, ensuring secure messaging and protection for personal data.
Enterprise Networks
Secure internal systems by deploying private services behind encrypted VPN channels, allowing only authorized users to access critical business resources.

Key Security Features
- Multi-Layer Access Security
- Mutual Authentication (mTLS)
- Post-Quantum Encryption
- Automated Certificate Management
- Global Secure Network Mesh
- Channel Isolation
